The Salmon Project: how to counter Internet censorship effectively using proxies with user trust levels

Governments in many countries restrict citizens' access to information and services on the Internet in one way or another. Combating such censorship is an important and difficult task. Usually simple solutions cannot boast about high reliability or long-term efficiency. More complex methods of overcoming blocks have disadvantages in terms of usability, low performance, or they do not allow you to maintain the quality of Internet use at the proper level.
A group of American scientists from the University of Illinois has developed a new method of overcoming blocks, which is based on the use of proxy technology, as well as segmenting users by trust level to effectively identify agents working for censors. We present you with the main theses of this work.
Description of the approach
Scientists have developed the Salmon tool, a system of proxy servers operated by volunteers from countries without restrictions on Internet use. In order to protect these servers from blocking by censors, the system uses a special algorithm for assigning a level of trust to users.
The method involves exposing potential censor agents that pose as ordinary users in order to find out the IP address of the proxy server and block it. In addition, countering Sybil attacks is carried out through the requirements to provide a link to a valid social network account when registering in the system or to receive a recommendation from a user with a high level of trust.
How it works
It is assumed that the censor is a state–controlled body that has the ability to take control of any router within the country. It is also assumed that the task of the censor is to block access to certain resources, and not to identify users for further arrests. The system cannot prevent such a course of events in any way – the state has plenty of opportunities to find out what services citizens use. One of them is the use of honeypot servers to intercept communications.
It is also assumed that the state has significant resources, including human ones. The censor can solve tasks that require hundreds and thousands of full-time employees.
A few more basic theses:
How I Replaced Gaming with Coding and Became a Web Developer

Today, I would like to share my personal story. I hope it helps you get to know me better and maybe benefits your own journey.
Utilizing Wearable Digital Health Technologies for Cardiovascular Monitoring

Wearable Digital Health Technologies for Monitoring in Cardiovascular Medicine
This review article presents a three-part true-life clinical vignette that illustrates how digital health technology can aid providers caring for patients with cardiovascular disease. Specific information that would identify real patients has been removed or altered. Each vignette is followed by a discussion of how these methods were used in the care of the patient.
New ChatGPT-4o: A Game-Changer That Could Replace Data Analysts, Demo Included

In this article, I’m going to discuss something really important. If you’re a data analyst or you want to learn data analysis, please watch this video till the end because it’s really important.
How to practice user empathy in UX design and make product more accessible
According to the Oxford Dictionary, empathy is “the ability to understand and share the feelings of another”. In UX, there is a special term “user empathy”. It refers to the ability of UX designers to fully understand what users need from a particular software product. Having user empathy and basing design solutions around users” comfort is one of the most true indicators of a designer”s professionalism. Without that, any product a designer works on has a high chance of turning out to be pointless. Apart from having empathy as a soft skill in general, there are several ways a designer can practice user empathy through different UX methods and techniques. In this article we would like to talk on how a UX designer can treat users with empathy and make the product more accessible for different groups of target audience.
VS Code Extensions You Need in 2024: My Top Picks

Welcome to my latest article. If you haven't caught my previous ones, I highly recommend checking them out for some really useful content. Today, I'm excited to dive into something special: my top 10 favorite VS Code extensions. These tools are incredibly popular among developers globally, and I believe they're essential for anyone serious about coding.
Top 10 Google Sheets Features to Enhance Your Productivity

It's been a while since my last appearance, but I'm excited to be back and to share something truly special with you. In this article, we'll explore my top 10 Google Sheets features that are guaranteed to boost your productivity, speed up your workflow, and make your data handling more efficient. So, without further ado, let's dive into these game-changing tools!
Simple complex programming

I always pay attention to assessing the complexity of programming in a particular language. Programming is indeed not an easy task and this is perceived as a fact and usually does not require any confirmation.
But the concept of “complexity” is akin to the term “heap”. For some, five coconuts is not so much, but for someone who ate one and “didn’t want any more,” this means that even one coconut will be too much for him.
The same goes for the complexity of programs. It seems that the constant increase in the complexity of programs is obvious to everyone and is observed in all areas of application of IT technologies, and programming languages themselves become more and more complex as they develop, but assessing “complexity” using numerical metrics is a problem. obviously a thankless task, but also “You can’t manage what you can’t measure...”
Typically, talk of “complexity” only implies value judgments without any numerical evaluation. And since I am personally interested in the issue of the complexity of programming languages, I decided to calculate the complexity of implementing the gcc compiler on some conditional “parrots”. What if we could see some patterns of difficulty changing over time?
Building blocks in programming languages
Practically all programming languages are built either on the principle of similarity (to make like this one, only with its own blackjack) or to realize some new concept (modularity, purity of functional calculations, etc.). Or both at the same time.
But in any case, the creator of a new programming language doesn't take his ideas randomly out of thin air. They are still based on his previous experience, obsession with the new concept and other initial settings and constraints.
Is there a minimal set of lexemes, operators, or syntactic constructs that can be used to construct an arbitrary grammar for a modern general-purpose programming language?
VERBAL CALCULATION (VC) IN EVIDENCE-BASED DSS AND NLP

S.B. Pshenichnikov
The article outlines a new mathematical apparatus for verbal calculations in NLP (natural language processing). Words are embedded not in a real vector space, but in an algebra of extremely sparse matrix units. Calculations become evidence-based and transparent. The example shows forks in calculations that go unnoticed when using traditional approaches, and the result may be unexpected.
The use of IT in Natural Language Processing (NLP) requires standardization of texts, for example, tokenization or lemmatization.
After this, you can try to use mathematics, since it is the highest form of standardization and turns the objects under study into ideal ones, for example, data tables into matrices of elements. Only in the language of matrices can one search for general patterns in data (numbers and texts).
If text is turned into numbers, then in NLP these are first natural numbers for numbering words, which are then embedded into real vectors is irreversible ed in a real vector space.
Perhaps we should not rush to do this but come up with a new type of numbers that is more suitable for NLP than numbers for studying physical phenomena. These are matrix hyperbinary numbers. Hyperbinary numbers are one of the types of hypercomplex numbers.
Hyperbinary numbers have their own arithmetic, and if you get used to it, it will seem more familiar and simpler than Pythagorean arithmetic.
In Decision Support Systems (DSS), the texts are value judgments and a numbered verbal rating scale. Next (as in NLP), the numbers are turned into vectors of real numbers and used as sets of weighted arithmetic average coefficients.
How blocking on the Internet works: an overview of modern methods using a real example
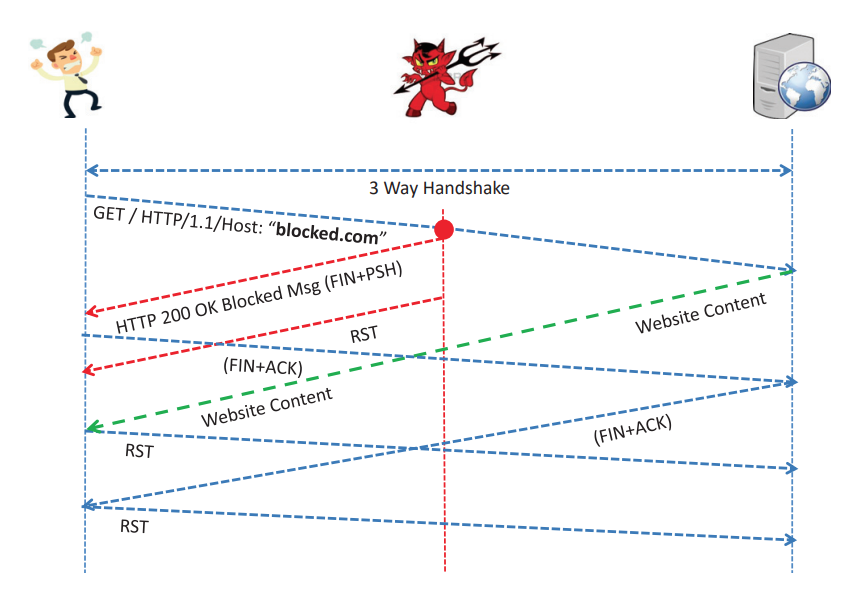
A group of Indian scientists has published an overview of modern methods of Internet blocking introduced by government agencies, using the example of their own country. They studied the mechanisms used by Internet service providers restricting access to prohibited information, assessed their accuracy, and the ability to bypass such blocks. We would like to bring to your attention the main theses of this work.
Possible solution to the problem of references in programming languages
Every programmer is familiar with the concept of "reference." This term usually refers to a small object whose main task is to provide access to another object physically located elsewhere. Because of this, references are convenient to use, they are easily copied, and they make it very easy to access the object to which the reference points, allowing access to the same data from different parts of the program.
Unfortunately, manual memory management, or more precisely, manual memory control, is the most common cause of various errors and vulnerabilities in software. All attempts at automatic memory management through various managers are hampered by the need to control the creation and deletion of objects, as well as periodically run garbage collection, which negatively affects application performance.
However, references in one form or another are supported in all programming languages, although the term often implies not completely equivalent terms. For example, the word "reference" can be understood as a reference as an address in memory (as in C++) and a reference as a pointer to an object (as in Python or Java).
Although there are programming languages that try to solve these problems through the concept of "ownership" (Rust, Argentum, or NewLang). The possible solution to these and other existing problems with references will be discussed further.
Enabling Cross-Process Dialogue with C# Sockets
In the ever-evolving landscape of software development, communication between processes has been a fundamental requirement since the inception of computer networking. As technology advanced, the need for efficient and reliable inter-process communication (IPC) mechanisms became increasingly crucial. One such mechanism that has stood the test of time is the socket.
Sockets trace their origins back to the early days of computer networking in the 1970s. The concept was first introduced in the Unix operating system by researchers at the University of California, Berkeley, as part of their work on the ARPANET project, which eventually evolved into the modern internet. Sockets were designed to provide a standardized interface for network communication, allowing processes to exchange data across different machines and networks.
Initially, sockets were primarily used for network programming tasks, such as building client-server applications and facilitating communication between distributed systems. However, their versatility soon became apparent, and sockets found their way into various domains, including inter-process communication (IPC) within a single machine.
Over the years, sockets have undergone numerous enhancements and standardizations, with the Berkeley Software Distribution (BSD) sockets becoming the de facto standard for network programming. This standard was later adopted by other operating systems, including Microsoft Windows, ensuring cross-platform compatibility and enabling widespread adoption.
In the world of software development, communication between processes is a common requirement, whether it’s a client-server architecture, distributed systems, or inter-process communication (IPC). Sockets provide a powerful mechanism for processes to exchange data efficiently and reliably. This article explores a simple implementation of a TCP client-server communication using sockets in C#, showcasing the versatility and robustness of this time-tested technology.
Unlocking Selenium Testing for Flutter's Web Apps
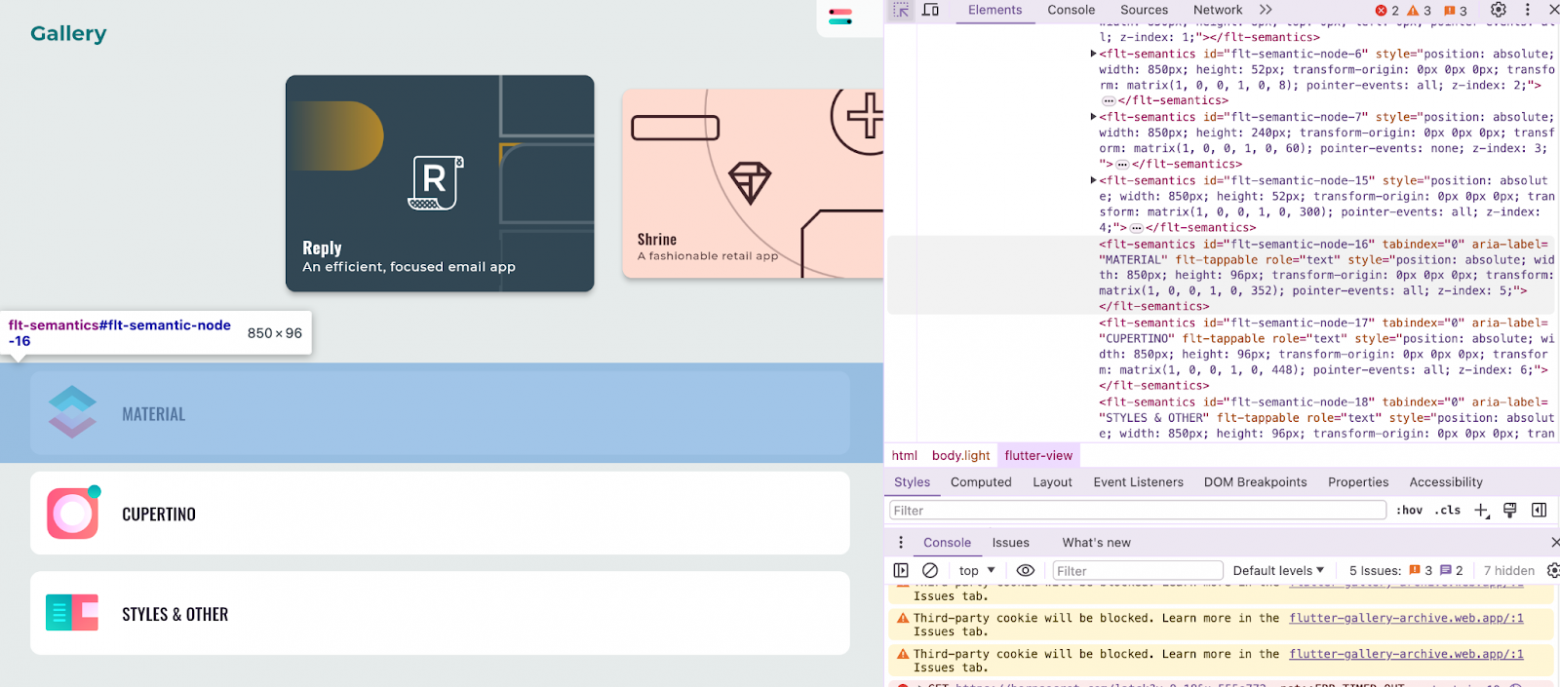
Navigating the intricacies of UI testing in the world of Flutter web applications can be a daunting task. If you've ever found yourself scratching your head, wondering how to apply your Selenium expertise to a Flutter-rendered interface, this article is for you. We're going to explore a method that bridges the gap between Flutter's unique rendering process and the robust testing capabilities of Selenium. Whether you're a seasoned tester or just starting out, the insights shared here will equip you with the knowledge to streamline your testing process and enhance the quality of your Flutter web apps. So, grab a cup of coffee, settle in, and let's unravel the mysteries of UI testing for Flutter web applications together.
Structure of Linux driver for single-board computer
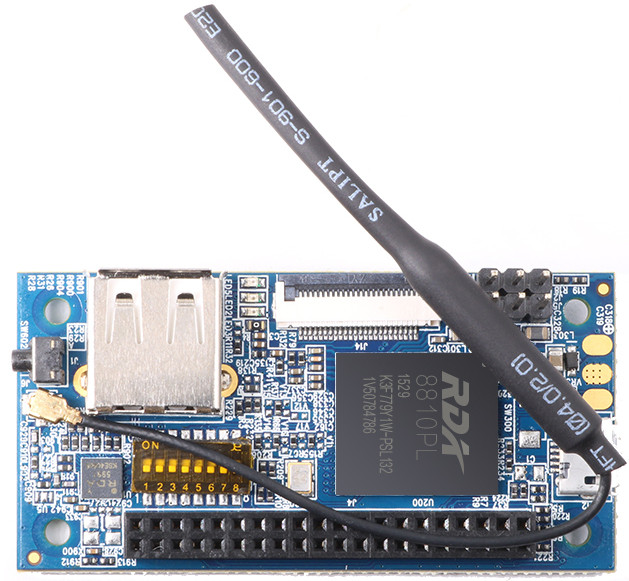
Hello my name is Dmitry. Recently I wrote article "Building firmware for Orange PI i96 (Orange PI 2g-iot) from scratch" . If you haven't read it yat, I highly recommend. And there I noticed that in order to build firware on current kernel, I have to rewrite drivers wirh new archetecture "Device tree". In this article I have revelate how I do it.
The new code as the side effect
The new code as the side effect
If we use the reducer function for form data handling It has an infinite list of returned values, which expands when the next development iteration updates the interface defining the form and implements a new field. So the reducer pattern is procedure code, not a functional
How to speed up Trendwatching with AI
Problem
Trendwatching is a powerful tool for driving strategic innovations. It helps to discover new teсhnologies, business models and products, that may be used for idea generation and technology transfer. It is a powerful tool for product managers, business stream managers, top managers and "strategists" and is mostly used on a regular basis.
How we took part in Ludum Dare
We are the Arcane Gaming development team, developing games since 2021. As of now, we have two major projects: Fanbattle and Suetologia. The time has come for us to take part in the Ludum Dare gaming hackathon for the first time.
Gatsby and its Greatness
In the internet’s early days, blogging was straightforward. A server with PHP and MySQL allowed you to share your thoughts globally. Even FTP access with an index.html file sufficed.
However, as the web evolved, so did blogging requirements. Non-programmers needed user-friendly web interfaces, faster loading times, and seamless daily publishing. Platforms like Reddit, WordPress, and Tumblr emerged, but they faced a common issue: website ownership.
Hubs
Authors' contribution
alizar 91982.8marks 24166.6ru_vds 20255.7alexzfort 14179.0XaocCPS 10986.2pronskiy 10649.4m1rko 10382.0ptsecurity 9631.2Andrey2008 9596.2Jeditobe 9387.6










